
Cyber Security Based Application Project
Develop an advanced security application that detects, monitors, and prevents unauthorized access or malicious activities. This project focuses on real-world network and data security practices.
Conducted under Texaaware Software Solutions, this project enables users to implement encryption, authentication, intrusion detection, and secure data transfer techniques using modern security tools.
Objectives: Design a secure application to protect sensitive data and monitor network activity.
Problem Statement: Data breaches and cyberattacks compromise the integrity and privacy of systems.
Significance: Ensuring system security helps maintain user trust and safeguard digital assets.
Technologies Used: Python, Flask, OpenSSL, Wireshark, MySQL, SHA-256, Cryptography Library.
Project Methodology

Key Highlights
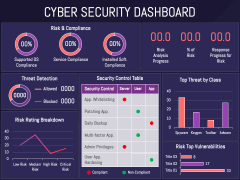
Project Results


Learning Outcomes
- Understanding of cybersecurity fundamentals
- Implementation of encryption and hashing techniques
- Development of secure login and monitoring modules
- Hands-on with Python security libraries
- Real-time threat monitoring and prevention


